Opinion
Transnistria: The Meltdown of a Frozen Conflict?
It is November 1990 and the river Nistru has a double value. For those situated on its right bank, the river is a boundary, a fronter meant to separate The Republic of Moldova from Transnistria. For those who reside on the left bank, the river is just a cross-point towards the most Eastern part of Moldova. The contention point is the existence or not of such a thing as an autonomous and sovereign Tranistrian state (PMR). At this point a war breaks down between the two sides,a pro-Moldavian force and the separatist one which had some military support from Russia. The open conflict ends with a cease-fire that has not been replaced by a more stable resolution since 1992.
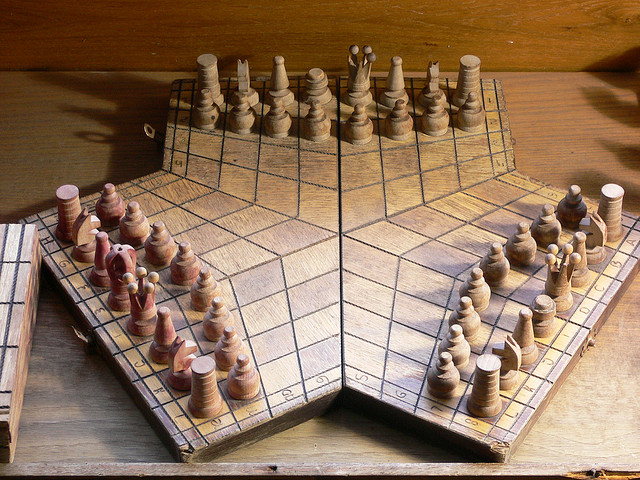
Back to present times, the Moldavian-Transnistrian relation is what we would call a ‘frozen conflict’. On the international level, the region between the Nistru river and Ukraine is recognized as being part of Moldova. In practice however, a filo-Russian centre of power exercises actual control over the disputed territory from its Tiraspol headquarters. I will argue that in a sense, this region is another chess board where NATO and Kremlin show off their skills.
There is an ongoing presence of Russian troops on the ground with the double moral purpose to protect Russian nationals from potential threats coming from the Moldavian majority and to help stabilize the situation in the form of peace-keeping. There is furthermore the strategic goal of maintaining an open door into Eastern Europe, following Kalinigrad’s example. If we imagined a dark scenario where the Old Continent would once more fall into violent conflict, the Kaliningrad exclave would play the part of a strategic military outpost for Russians, which could be further supplied with weapons and soldiers through the Baltic Sea.
The same logic could have been applied to PMR until the current Ukrainian turn of events. As I see it, Ukraine stands between this potential outpost and the Russian Federation. Events in Ukraine bring to light at the least the possibility of a future NATO membership. That translates into the blockage of access to Transnistria for Kremlin’s hard power capabilities. Metaphorically it resembles the clogging of an artery which eventually leads to the death of an organ. The strategic benefit of Transnistria will be lost if Kiev-Moscow relations get interrupted. As a consequence, Russian leaders point now their energy on another outpost in the Black Sea, which is Crimea.
An example that proves all the above is the recent diplomatic scuffle between Romania and Moldova on one side and the Russian Deputy Prime Minister, Rogozin. The latter one was intending to fly to Tiraspol for the Victory Day celebration. Since Ukraine and Romania blocked their airspace to the plane on which he was travelling, Rogozin was stuck in Moldova. He managed eventually to return to Moscow, from where he made serious threats to Romanian authorities: ”Next time I’ll fly on board TU-160”. That is Russia’s largest bomber.
It is being said that Rogozin carried with him back home the signed petitions of Transnistrian residents which claim the recognition of their half-a-million-people Republic as independent and autonomous from Moldova. The relation between the two is now at a very low point both because of Russia’s support for PMR independence and also because of EU’s decision to sign the association agreements with the authorities in Chisinau and Tbilisi. The existing pattern shows that most Eastern and Southeastern European countries were admitted into the EU only after being granted NATO membership. If the habitual way of handling EU enlargement does not change, then there is a high probability that Moldova, Ukraine and Georgia will in the foreseeable future have NATO troops on their territories. Under such circumstances, Article 5 will enforce itself directly against Russia in the case of any type of aggression towards the mentioned countries. The West will have the responsibility to act militarily.
Finally, this big power politics explains the recognition movement undergoing in Transnistria. Its parliament is on the path of recognizing Russian legislation as applicable to its citizens who will officially have the Russian language as their national language. These are preparatory steps for being part of the Russian Federation, a desire expressed openly by Transnistrian officials. Nevertheless, prior to Moldova moving a step closer to the EU, Russian politicians appeared a bit reserved in accepting Tiraspol’s offers. Some even went as far as to say that Chisinau is behaving properly in observing the cease-fire and the truce and that only a reunification with Romania would automatically call for a solution as dramatic as annexation. This fear was as a matter of fact probably the main cause for the secessionist move in the first place. Aside from this, most probably it will very much depend on the results of the election for new leaders in Kiev and the situation on the ground in Eastern Ukraine. More than this, it will be conditioned by the love and hate relationship between the EU and the US which materializes in NATO’s strategy.
To conclude our discussion, we can sum up and observe the main antagonists and their interests. First, we have the opposition between Moldova and Tiraspol on PMR’s right of self-determination . Going on a higher level, we have Romania who sees itself as a gateway to Europe and therefore must act as a responsible, strong actor in the face of any potential threat coming from its East. On the big power playing field, we have Russia who is feeling pressured from NATO and US expanding their grip towards its borders. Finally we have the EU and its member states who have a very strong interest in creating a free market that would incorporate the countries around the Black Sea and also an existential need of finding alternative energy supplies, mainly from Azerbaijan, supplies which would cross Georgia and even Ukraine. These are the conditions that will shape Transnitria’s fate and with it most certainly everyone’s future. The heat is increasing around this frozen conflict and its meltdown will unfortunately bring a big flood with it.
China
Nepal Hindu Rashtra: Time to Wrap Up Communism?

Nepal abolished the Constitutional Monarchy in May 2008 and declared itself as a Federal Democratic Republic. There was a new hope in Nepal as it was becoming world’s newest democracy even though it had dissolved the Hindu Rashtra. However, the democracy in Nepal immediately got into the tight grips of leftists and communists backed by China. It has been almost 12 years since monarchy was abolished in Nepal. Interestingly, the Himalayan country has already seen 11 Prime Ministers in this period. Thus, leaving the Nepalese people still yearning for good and stable governance.
Re-establish Hindu Rashtra
As the political instability is growing in Nepal, people are demonstrating concerns about the future of the country. In fact, Nepalese citizens are unhappy with frequent interference by China and India influencing its unstable communist regime. More voices are now growing in support of reinstating the Monarchy and declaring Nepal as world’s only Hindu Rashtra (which by default offers full religious freedom to other religious minorities as per Hindutva concept of Sarva Dharma Sama Bhava – all paths lead to one).
Former Deputy Prime Minister of Nepal, Kamal Thapa said that if political parties do not recognize the seriousness of reinstating the monarchy, then the country will head for a period of darkness. “Recently, we’ve had high-ranking officials from India and China come to Nepal to try and solve problems within the ruling party,” he said. “We cannot let others dictate what we want to do.”
Communist Party All Set to Suppress Protests, By Force
Kamal Thapa has firmly demanded an all party meet to discuss reinstating of monarchy. Throughout the month of December, 2020 Nepal has seen anti communism protests across the country in support of reinstating the monarchy and Hindu Rashtra. Most importantly, the demand has become a nationwide mass people’s movement. So much so that the communist regime had to send a directive to 77 districts in 7 provinces. The directive suggests suppressing the protests by force. Nevertheless, Rashtriya Prajatantra Party and other royalist groups have ignored this threat from the communist regime. Protester groups have pledged to strengthen the protest in the coming weeks.
Nepal: Demonstration held in capital Kathmandu, demanding restoration of monarchy in the country. pic.twitter.com/TFjmKu9U9Z
— ANI (@ANI) December 5, 2020
Role of China – Hope for Communism in Nepal
China’s ambassador to Nepal is known to have very close relationship with Nepalese Communist regime. In fact, She has been super effective in tilting Nepal’s posture towards its ideological partner, China. One of her greatest achievements in 2020 was artificially manufacturing a border conflict between Nepal and India. Consequently, souring relations between the two Hindu majority nations. In addition, she managed to silence Nepal’s communist government after China took one of Nepal’s border villages under its control. However, recent political turmoil in Nepal and a renewed demand for reinstating of Hindu Monarchy is showing that the situation is now out of Chinese hands
Role of India
Year 2020, was not a good year for India and Nepal relations. India was busy in controlling domestic Covid cases. On the other hand, China had launched an invasive campaign into Indian territory. In addition, India is always busy with Pakistan on its western borders. However, the surprise came to India when China was almost successful in creating a new border tension between India and Nepal.
Those who do not know about Indian government should note that the current ruling party in India finds itself ideologically opposite to communism. This further creates differences between the two countries.
Communist party in Nepal has blamed India for supporting the ongoing anti communism protests in Nepal. However, former advisor to Nepal’s PM has suggested there is no proof that India is fueling pro Monarchy, anti communism demand in Nepal.
Nevertheless, There are certain influencers in India who have, in their personal capacity, expressed support for reinstating the Hindu monarchy. Yogi Adityanath, who is the Chief Minister of an Indian state bordering Nepal, said in 2015 that Nepal should declare itself a Hindu Monarchy. Readers should note that in 2015 Yogi Adityanath was not the Chief Minister yet. However, today he is not only popular in south of Nepal, his popularity is growing in Nepal as well.
Will The World See the first Hindu Rashtra?
It is difficult to answer this question at this moment. However, Nepalese communist government could not resolve the political instability and in December 2020 Nepalese government dissolved the parliament. Nepal will see next elections in April – May 2021. Hopefully, the world will see Nepal’s 12th Prime Minister in 13 years or may be a Hindu King? Royalists and protester groups have expressed confidence in winning next elections. We have our eyes on Nepal for updates.
Opinion
America’s Justice System – The Need For Reform

A recent poll by the National Opinion Research Centre revealed that 95% of Americans favour vital criminal justice reforms. This is hardly surprising, given that several people of varying racial, partisan and ideological dispositions have called out the justice system over its many failures throughout the years. Most Americans received the Trump Administration’s First Step Act as a step in the right direction, as about 60% of people approved the criminal justice reform bill according to a 2018 poll. However, many people still believe the justice system’s approach to crime is ineffective and needs dire change, and these are some reasons why.
Prison population and funding concerns
Research conducted revealed America has about 2.3 million prisoners, making the US the country with the highest incarceration rate globally. Experts estimate that the country’s prison population has grown by a whopping 340% over the past three decades; new prisoner admissions into jails are higher than prisoner release numbers. The cost of maintaining the nation’s prisons at taxpayers’ expense has inspired a lot of backlash and calls for budget cuts. According to research, slashed correction spending was the preferred option by most states to balance their budgets and redirect spending to other areas.
Minimum mandatory sentences
Minimum mandatory sentences are statutes that force judges to give defendants convicted of a crime the minimum prison sentence. Mandatory sentences rob judges of the traditional way of considering the defendant’s character and the unique circumstances surrounding offences. Even when represented by criminal defense attorneys with many years’ experience, defendants often succumb to prosecutors’ pressure to plead guilty or face more severe charges with higher mandatory sentences. The guilty plea bargain consequently resolves about 95% of both federal and state court cases. Research also shows that about half of inmates in federal prisons are doing time for drug offences- causing overpopulation in the prison system.
Growing number of people killed by the police
An estimated 1000 civilians are killed by police officers annually in the US. The frequency of police brutality cases over the years requires immediate reform to the American justice system. Data suggests that the incidence of fatal police shootings is higher among African-Americans than any other ethnicity, inspiring movements like the ‘Black Lives Matter’ campaign to press on with protests for significant police etiquette reforms towards coloured minorities. The police force faces incessant accusations of racial profiling, indiscriminate use of power, and poor discretion, which has led a reported 58% of Americans to think policing needs major reforms through measures like better-trained officers, and wearing body cameras.
Evolving public opinion on crime
Research released by the Sentencing Project and The Justice Policy Institute reveals that more people in conservative states are embracing preventive, rehabilitative, and alternative sentencing options for non-violent offenders. Most Americans now view the prevention of crime as the most vital function of the justice system, as 77% of Americans think that focusing more on character education and after-school programs would be cost-effective by reducing the number of people going to jail. Almost two-thirds of Americans also believe in the need for lighter sentences with more useful, reformative programs in prisons that will benefit inmates upon release. Therefore, support for harsh penalties that harden criminals and make them a more significant menace when reintroduced into society has dwindled.
Opinion
The History Question: Is It Better to Remember or to Forget?

Years ago, a philosopher by the name of George Santayana said a phrase that fuels many debates to this day. His original saying is “those who cannot remember the past are condemned to repeat it”, although, many sources now present it as variations of “those who cannot learn from history are doomed to repeat it”. The latter definitely has more substance to it in the light of the ongoing debate about how much history we should be learning and how.
Is It Better to Remember or Forget About the Past?
On one hand, Santayana was right. Learning about the past is essential in order for people to progress. One also shouldn’t overlook the importance of remembrance and paying respects to the dead, both those who pushed the progress forward and those who have fallen victims to major tragedies that could and should have been averted.
The main argument in favor of learning about the past is that its knowledge is necessary for preventing the same thing happening in the future. Having it one can see the signs and stop the tragedy before it gains momentum.
That’s sound in theory, but the reality is always different. For example, today people are surely forgetting, and the much-critiqued education system is only partially at fault here. Even the greatest of tragedies weren’t spared this fate. It’s a proven fact that about two-thirds of millennials today don’t know about the Holocaust, and this number is surely greater for generations that follow them. In the school history course, the subject of one of the greatest disasters in history is barely touched, if touched at all. And outside of a history classroom, one can only see small, but terrifying, glimpses of it at the Holocaust Museum and other museums that rarely attract many visitors. And now we are witnessing a rise of antisemitic crime.
Are these two facts related? Does the lack of awareness about the horrors done in the name of Aryan supremacy contribute to the fact that right-winged extremists seem to be gaining popularity again?
It does, but by how much? That is the question that no one can truly answer.
And what about other genocides? The Holocaust had the highest death toll, but it was far from the only genocide in history. And quite a few of those happened after World War 2 and before the memory of the atrocities against the Jews began to fade. This means that while forgetting history is a factor, it’s not the deciding factor in its repeats.
But what is that thing responsible for the reenactment of past mistakes and tragedies?
Learning. This is the important thing that is most often overlooked when citing Santayana’s famous saying. It’s not enough to learn about the past and know the facts of things that happened. It’s important to learn from those facts and put in place protections that will prevent them from happening again. And this is something that humanity, as a whole, has yet to succeed in doing.
Dwelling in the Past Can Be Just As Bad
One also shouldn’t forget that there is such a thing as “too much history”. The Bosnian War and genocide that happened there in the 1990s is a vivid example of how the past can be exploited by political powers. Used as a part of propaganda, which fueled the war, history can become a weapon in the hands of those who want to use it for their own goals.
And this is what humans have been doing since the dawn of time. There is always someone who will use any means necessary to achieve whatever it is they wish. This results in wars and genocides, and hundreds of smaller but no less devastating tragedies.
Therefore, the problem isn’t whether people should be learning history but human nature itself. Perhaps, teaching this can help fix this fundamental flaw and truly stop the worst of the past from repeating.