Opinion
BRICS Summit 2012: A long Journey to cover; Overview, Outcomes and Expectations
 |
| BRICS Summit 2012 Logo |
Leaders from Brazil, Russia, India, China and South Africa met on Thursday, Mar 29, 2012 in Delhi for the fourth annual Summit. Earlier known as BRIC before the addition of South Africa, BRICS is the group of emerging economies around the world, who are exploring new ways of collaboration, collective economic growth and developing common ground on foreign policy.
 |
| Sao Paulo, Brazil |
 |
| Moscow, Russia |
The summit stressed on linking economies, as in trading in local currencies as well as linking stock exchanges of the member countries. The leaders also stressed on setting up of an international bank on par with Asian Development Bank, IMF and World Bank. It would fund various development projects in member countries and other emerging economies and may act as a relief provider for first time buyer mortgages in case of real financial crisis and disaster. The goal of the bank will also include lending, in the long term, if there comes a global financial crises such as the Eurozone crisis and issuing convertible debt, which could be bought by the central banks of all the member nations. Hence it will be acting as a vessel for risk-sharing.
 |
| Mumbai, India |
 |
| Shanghai, China |
The idea of setting up such bank was put forward by India, which received a good response from the member countries as well as from the countries who were observing the event carefully. Analyst John Mashaka called India’s move “long overdue”, and said that setting up a bank was a means of “pulling out of the western-dominated World Bank and the International Monetary Fund.” Assistant professor at the Institute of African Studies (China) Yuhua Xiao noted that setting up the bank showed signs of growing self-assertiveness and inter-dependence among developing economies. Dr. Alexandra A Arkhangelskaya noted that creating such a bank would effectively “shift the weight of economic power”, and could also be very beneficial to non-BRICS nations.
 |
| Johannesburg, South Africa |
The nations also signed an agreement to extend credit facilities in their local currencies, a step to reduce the role of dollar between them. As of now, if Russia wants to trade with India, Russia will convert Rubles to Dollars send it to India, and then India will convert Dollars to Rupees. Completely removing the intermediate step of converting to and from dollar is not so easy, but if removed, the trade between the two countries will become independent of what the value of dollar is, which is highly unstable.
Also the nations will be launching a benchmark equity index derivatives that would allow investor of one member country to bet on the performance of stock exchanges of other member countries without currency risk.
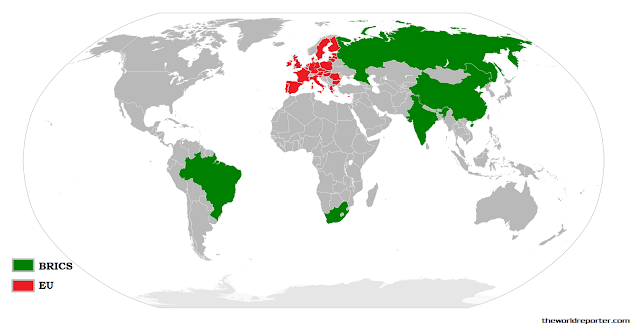
Accounted 50% of global economic growth in last decade, BRICS accounts for 26% of global landmass, 42% of the global population and 40% of global GDP.
Below is the tabulation of the countries and their economy in therms of GDP (PPP). The data is taken from CIA World Factbook GDP PPP data update of 2011. PPP is one of the scale to measure difference between two economies. Using a PPP basis is arguably more useful when comparing generalized differences in total economic output between countries because PPP takes into account the relative costs and the inflation rates of the countries, rather than using just exchange rates, which may distort the real differences in income. The table shows BRICS as a single entity is more powerful than European Union. The data for GDP at purchasing power parity (PPP) has also been re based using the new International Comparison Program (ICP) price surveys and extrapolated to 2007. Final figures are estimates in billions of international dollars.
| Rank | Country | GDP (PPP) $Billion | Year |
|---|---|---|---|
| — | BRICS | 20,975 | 2011 est. |
| — | 15,390 | 2011 est. | |
| 1 | 15,040 | 2011 est. | |
| 2 | 11,300 | 2011 est. | |
| 3 | 4,463 | 2011 est. | |
| 4 | 4,389 | 2011 est. | |
| 5 | 3,085 | 2011 est. | |
| 6 | 2,373 | 2011 est. | |
| 7 | 2,284 | 2011 est. | |
| 8 | 2,250 | 2011 est. | |
| 9 | 2,214 | 2011 est. | |
| 10 | 1,826 | 2011 est. |
Another method of measuring economy is GDP (nominal) based on official exchange rates. The list below includes mostly 2011 estimates from the CIA World Factbook. The table shows BRICS as the third largest economy after EU and US.
| Rank | Country | GDP nominal $Billion | Year |
|---|---|---|---|
| — | 17,720,000 | 2011 est. | |
| 1 | 17,720,000 | 2011 est. | |
| — | BRICS | 13,766,000 | 2011 est. |
| 2 | 6,988,000 | 2011 est. | |
| 3 | 5,866,000 | 2011 est. | |
| 4 | 3,739,000 | 2011 est. | |
| 5 | 2,919,000 | 2011 est. | |
| 6 | 2,407,000 | 2011 est. | |
| 7 | 2,370,000 | 2011 est. | |
| 8 | 2,135,000 | 2011 est. | |
| 9 | 1,995,000 | 2011 est. | |
| 10 | 1,954,000 | 2011 est. |
The performance of the BRICS nations on the international platform has been brilliant, despite the fact all these countries come from different continents, having different government, political and economical structure. How far this concept of BRICS will sustain no body knows, but if it works then it will bring a great change in the current world, a change for good.
The countries have been working together to find some common ground and fortunately their thoughts match on the issues of West Asia, North Africa and Afghanistan. All five countries called for the international community to continue development projects in Afghanistan for 10 years after America led international forces will withdraw from the nation by the end of 2014.
BRICS nations together have strongly condemned the Western world’s politics on Iran to make other countries stick to the restrictions imposed by them on trade ties. China’s Trade Minister Chen Deming said that the “rise [in the price] of crude oil has impacted all countries. The Iran issue has become an issue for all. We need to continue with normal relations with Iran, but, at the same time, we respect UN resolution. We hope that unilateral movement by one country will not affect other countries.” The group warned against any military intervention in Syria by the West or by Israel in Iran. They added that a war with Iran would have “disastrous consequences.”
Out of five BRICS nations, three of them have remained or are super power. India before 14th century, Russia in the 20th century and China almost in 21st century. No matter these countries possess power and wealth, but they may not share good relations with each other. Brazil and South Africa being geographically isolated from these nations share good relations with all. The best example is China and India, both of them have faced each other in the war in 1965 and China is still occupying a large part of North India and claims some part of Indian territory in North East India. China was also about to open the front in Indo Pakistani war in 1971 but didn’t do so, fearing Pro Indian Soviet Union might take action against them. Russia and China have also shared cold relations following the illegal migration of Chinese in Russia’s far east and border dispute which was recently resolved.
Russia and India have been sharing good relations from the Soviet times. India also shares good relations with South Africa, one of the major reason being Mahatma Gandhi, whose work in South Africa promoted equality between blacks and whites. In South Africa, Mahatma Gandhi is equally respected as in India. Brazil has also been close to all the countries.
Leaving aside all these solid claims about BRICS, there are critics as well who discuss why BRICS might fail with some genuine facts. One of the reason is all these countries come from different continents, different social, economical and political systems and some of these countries do not share good relations as well as common ground.
One of the best example of this claim is that after the declaration of setting up of an International bank, these countries fear that China will be the most benefited country out of all and will enjoy the most.
However, just after the summit was over, India and China declared that they will keep their border issue aside for now and will take more steps to increase trade between the two neighbors. Indian government also expressed their interest in inviting Chinese investment in India’s manufacturing sector. Both the countries have together declared this year as Indo Chinese year of friendship and cooperation.
After the summit, Brazil and India also took the opportunity of exploring their way of cooperation. The two countries signed six pacts in areas ranging from closer cooperation in science and biotechnology to cultural exchanges. Under a signature, Brazilian initiative Science Without Borders, the two sides inked a pact that envisages placement of Brazilian students and young researchers in India. It will be funded by Brazil.
US State Department spokesman Mark Toner said, “We reviewed the leaders’ Delhi declaration and believe that their efforts to engage in global multilateral institutions productively can only strengthen the international system. United States welcomed the efforts by the so-called BRICS — Brazil, Russia, India, China and South Africa — to support the recovery of the global economy as well as “
China
Nepal Hindu Rashtra: Time to Wrap Up Communism?

Nepal abolished the Constitutional Monarchy in May 2008 and declared itself as a Federal Democratic Republic. There was a new hope in Nepal as it was becoming world’s newest democracy even though it had dissolved the Hindu Rashtra. However, the democracy in Nepal immediately got into the tight grips of leftists and communists backed by China. It has been almost 12 years since monarchy was abolished in Nepal. Interestingly, the Himalayan country has already seen 11 Prime Ministers in this period. Thus, leaving the Nepalese people still yearning for good and stable governance.
Re-establish Hindu Rashtra
As the political instability is growing in Nepal, people are demonstrating concerns about the future of the country. In fact, Nepalese citizens are unhappy with frequent interference by China and India influencing its unstable communist regime. More voices are now growing in support of reinstating the Monarchy and declaring Nepal as world’s only Hindu Rashtra (which by default offers full religious freedom to other religious minorities as per Hindutva concept of Sarva Dharma Sama Bhava – all paths lead to one).
Former Deputy Prime Minister of Nepal, Kamal Thapa said that if political parties do not recognize the seriousness of reinstating the monarchy, then the country will head for a period of darkness. “Recently, we’ve had high-ranking officials from India and China come to Nepal to try and solve problems within the ruling party,” he said. “We cannot let others dictate what we want to do.”
Communist Party All Set to Suppress Protests, By Force
Kamal Thapa has firmly demanded an all party meet to discuss reinstating of monarchy. Throughout the month of December, 2020 Nepal has seen anti communism protests across the country in support of reinstating the monarchy and Hindu Rashtra. Most importantly, the demand has become a nationwide mass people’s movement. So much so that the communist regime had to send a directive to 77 districts in 7 provinces. The directive suggests suppressing the protests by force. Nevertheless, Rashtriya Prajatantra Party and other royalist groups have ignored this threat from the communist regime. Protester groups have pledged to strengthen the protest in the coming weeks.
Nepal: Demonstration held in capital Kathmandu, demanding restoration of monarchy in the country. pic.twitter.com/TFjmKu9U9Z
— ANI (@ANI) December 5, 2020
Role of China – Hope for Communism in Nepal
China’s ambassador to Nepal is known to have very close relationship with Nepalese Communist regime. In fact, She has been super effective in tilting Nepal’s posture towards its ideological partner, China. One of her greatest achievements in 2020 was artificially manufacturing a border conflict between Nepal and India. Consequently, souring relations between the two Hindu majority nations. In addition, she managed to silence Nepal’s communist government after China took one of Nepal’s border villages under its control. However, recent political turmoil in Nepal and a renewed demand for reinstating of Hindu Monarchy is showing that the situation is now out of Chinese hands
Role of India
Year 2020, was not a good year for India and Nepal relations. India was busy in controlling domestic Covid cases. On the other hand, China had launched an invasive campaign into Indian territory. In addition, India is always busy with Pakistan on its western borders. However, the surprise came to India when China was almost successful in creating a new border tension between India and Nepal.
Those who do not know about Indian government should note that the current ruling party in India finds itself ideologically opposite to communism. This further creates differences between the two countries.
Communist party in Nepal has blamed India for supporting the ongoing anti communism protests in Nepal. However, former advisor to Nepal’s PM has suggested there is no proof that India is fueling pro Monarchy, anti communism demand in Nepal.
Nevertheless, There are certain influencers in India who have, in their personal capacity, expressed support for reinstating the Hindu monarchy. Yogi Adityanath, who is the Chief Minister of an Indian state bordering Nepal, said in 2015 that Nepal should declare itself a Hindu Monarchy. Readers should note that in 2015 Yogi Adityanath was not the Chief Minister yet. However, today he is not only popular in south of Nepal, his popularity is growing in Nepal as well.
Will The World See the first Hindu Rashtra?
It is difficult to answer this question at this moment. However, Nepalese communist government could not resolve the political instability and in December 2020 Nepalese government dissolved the parliament. Nepal will see next elections in April – May 2021. Hopefully, the world will see Nepal’s 12th Prime Minister in 13 years or may be a Hindu King? Royalists and protester groups have expressed confidence in winning next elections. We have our eyes on Nepal for updates.
Opinion
America’s Justice System – The Need For Reform

A recent poll by the National Opinion Research Centre revealed that 95% of Americans favour vital criminal justice reforms. This is hardly surprising, given that several people of varying racial, partisan and ideological dispositions have called out the justice system over its many failures throughout the years. Most Americans received the Trump Administration’s First Step Act as a step in the right direction, as about 60% of people approved the criminal justice reform bill according to a 2018 poll. However, many people still believe the justice system’s approach to crime is ineffective and needs dire change, and these are some reasons why.
Prison population and funding concerns
Research conducted revealed America has about 2.3 million prisoners, making the US the country with the highest incarceration rate globally. Experts estimate that the country’s prison population has grown by a whopping 340% over the past three decades; new prisoner admissions into jails are higher than prisoner release numbers. The cost of maintaining the nation’s prisons at taxpayers’ expense has inspired a lot of backlash and calls for budget cuts. According to research, slashed correction spending was the preferred option by most states to balance their budgets and redirect spending to other areas.
Minimum mandatory sentences
Minimum mandatory sentences are statutes that force judges to give defendants convicted of a crime the minimum prison sentence. Mandatory sentences rob judges of the traditional way of considering the defendant’s character and the unique circumstances surrounding offences. Even when represented by criminal defense attorneys with many years’ experience, defendants often succumb to prosecutors’ pressure to plead guilty or face more severe charges with higher mandatory sentences. The guilty plea bargain consequently resolves about 95% of both federal and state court cases. Research also shows that about half of inmates in federal prisons are doing time for drug offences- causing overpopulation in the prison system.
Growing number of people killed by the police
An estimated 1000 civilians are killed by police officers annually in the US. The frequency of police brutality cases over the years requires immediate reform to the American justice system. Data suggests that the incidence of fatal police shootings is higher among African-Americans than any other ethnicity, inspiring movements like the ‘Black Lives Matter’ campaign to press on with protests for significant police etiquette reforms towards coloured minorities. The police force faces incessant accusations of racial profiling, indiscriminate use of power, and poor discretion, which has led a reported 58% of Americans to think policing needs major reforms through measures like better-trained officers, and wearing body cameras.
Evolving public opinion on crime
Research released by the Sentencing Project and The Justice Policy Institute reveals that more people in conservative states are embracing preventive, rehabilitative, and alternative sentencing options for non-violent offenders. Most Americans now view the prevention of crime as the most vital function of the justice system, as 77% of Americans think that focusing more on character education and after-school programs would be cost-effective by reducing the number of people going to jail. Almost two-thirds of Americans also believe in the need for lighter sentences with more useful, reformative programs in prisons that will benefit inmates upon release. Therefore, support for harsh penalties that harden criminals and make them a more significant menace when reintroduced into society has dwindled.
Opinion
The History Question: Is It Better to Remember or to Forget?

Years ago, a philosopher by the name of George Santayana said a phrase that fuels many debates to this day. His original saying is “those who cannot remember the past are condemned to repeat it”, although, many sources now present it as variations of “those who cannot learn from history are doomed to repeat it”. The latter definitely has more substance to it in the light of the ongoing debate about how much history we should be learning and how.
Is It Better to Remember or Forget About the Past?
On one hand, Santayana was right. Learning about the past is essential in order for people to progress. One also shouldn’t overlook the importance of remembrance and paying respects to the dead, both those who pushed the progress forward and those who have fallen victims to major tragedies that could and should have been averted.
The main argument in favor of learning about the past is that its knowledge is necessary for preventing the same thing happening in the future. Having it one can see the signs and stop the tragedy before it gains momentum.
That’s sound in theory, but the reality is always different. For example, today people are surely forgetting, and the much-critiqued education system is only partially at fault here. Even the greatest of tragedies weren’t spared this fate. It’s a proven fact that about two-thirds of millennials today don’t know about the Holocaust, and this number is surely greater for generations that follow them. In the school history course, the subject of one of the greatest disasters in history is barely touched, if touched at all. And outside of a history classroom, one can only see small, but terrifying, glimpses of it at the Holocaust Museum and other museums that rarely attract many visitors. And now we are witnessing a rise of antisemitic crime.
Are these two facts related? Does the lack of awareness about the horrors done in the name of Aryan supremacy contribute to the fact that right-winged extremists seem to be gaining popularity again?
It does, but by how much? That is the question that no one can truly answer.
And what about other genocides? The Holocaust had the highest death toll, but it was far from the only genocide in history. And quite a few of those happened after World War 2 and before the memory of the atrocities against the Jews began to fade. This means that while forgetting history is a factor, it’s not the deciding factor in its repeats.
But what is that thing responsible for the reenactment of past mistakes and tragedies?
Learning. This is the important thing that is most often overlooked when citing Santayana’s famous saying. It’s not enough to learn about the past and know the facts of things that happened. It’s important to learn from those facts and put in place protections that will prevent them from happening again. And this is something that humanity, as a whole, has yet to succeed in doing.
Dwelling in the Past Can Be Just As Bad
One also shouldn’t forget that there is such a thing as “too much history”. The Bosnian War and genocide that happened there in the 1990s is a vivid example of how the past can be exploited by political powers. Used as a part of propaganda, which fueled the war, history can become a weapon in the hands of those who want to use it for their own goals.
And this is what humans have been doing since the dawn of time. There is always someone who will use any means necessary to achieve whatever it is they wish. This results in wars and genocides, and hundreds of smaller but no less devastating tragedies.
Therefore, the problem isn’t whether people should be learning history but human nature itself. Perhaps, teaching this can help fix this fundamental flaw and truly stop the worst of the past from repeating.